Applies to Platform: UTM 3.0.X and later; 4i Edge 3.0 and later
Last Update: 24th January 2025
This lesson guides you in the configuration of an Endian Appliance for accessing an Active Directory Server. The AD server can be accessed either as LDAP or NTML and used as a provider to authenticate users for various services running on an Endian UTM Appliance: HTTP Proxy, OpenVPN, IPsec L2TP, and IPsec XAUTH. This lesson illustrates both methods, using the same AD server.
Prerequisites
Before starting this lesson, make sure that:
- HTTP Proxy needs to be enabled when trying AD join.
- The Endian Appliance can access the AD server
- The clock on the AD server and the Endian Appliance are synchronised (this should always be the case, since both system use ntp)
- You have all necessary information (domain name, username, passwords, and so on) to access the AD Server. If you are unsure, the next section shows how to retrieve all these information.
- A running instance of either the HTTP proxy or a VPN service (i.e., an OpenVPN server instance or IPsec with either L2TP or XAUTH).
Throughout this lesson we will use an AD Server called services.example.com, located at the IP address 10.12.34.56.
Retrieving information from the AD Server
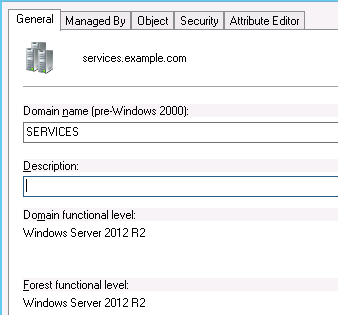
The screenshot above shows the properties of a Domain. From here we need the name of the domain (services.example.com, shown at the top of the image next to the icon) and the legacy domain name (services).
The additional information needed can be found by issuing the command nltest /dsgetdc: from the Windows' command line (or the power shell), like shown in the screenshot below:
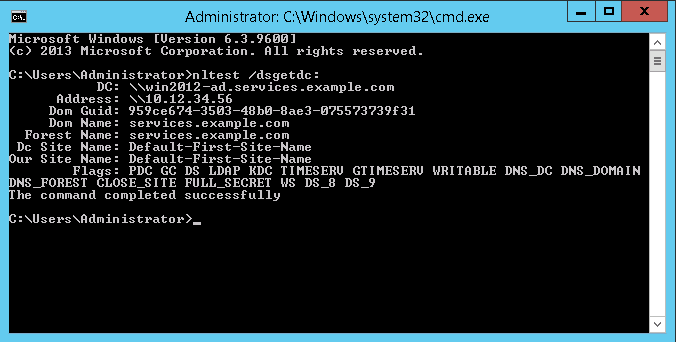
Here, we find the PDC hostname (the first word of the line starting with DC:, win2012-ad), the IP address of the AD server (10.12.34.56).
Note
The distinguished names (DN) can be retrieved using the dsquery tool from the command line in the LDAP server, for example:
C:\Users\Administrator>dsquery user domainroot
and
C:\Users\Administrator>dsquery group domainroot.
Connecting to AD using NTLM
This method can be used with the HTTP Proxy only.
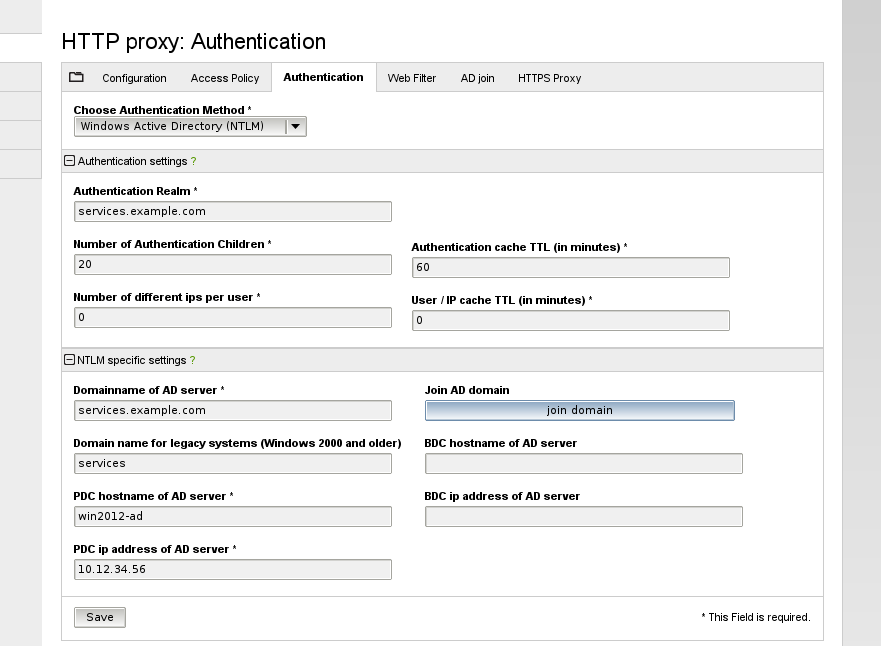
For a successful connection it is necessary to know the following information:
- The Authentication Realm: services.example.com.
- The domain name of the AD server, which is in most cases, the same as the Authentication Realm.
- If the AD Server is a pre-2000 version, the domain name for legacy systems. In our case, this is services.
- The Primary Domain Controller Hostname of the AD server and its IP Address.
Once all these options have been configured, it is possible to click on Save to store the configuration on disk and start the connection to the LDAP server.
Verify connection and troubleshooting
In order to test the configuration made, first we have to configure the PC to use the proxy. When using NTLM authentication each network we want filtered should be set to "non-transparent". Also we want to have all web access (allowed and blocked) logged for review purposes, so we're going to enable the appropriate logging options. The necessary steps are presented in the following screen:
Configure the Content Filter Profile
We will configure 2 profiles: one for the general users group and the second one for the admin group.
The first profile will be more restrictive regarding we access and for this example, we configured only web filtering by URL Blacklist (only) for ease and administration purposes. The 2 profiles are shown in the screens below:
Profile for general users group
Profile for admin group
Configure the Access Policy
The last step is to create access policy rules which will map the content filtering profile based on a specific network configuration. The first rule we're creating is a policy for any zone for users in the "general users" group that uses the content filtering profile userprofiler.
The second rule is for admin users and it is created similarly with the first one.
Setup Client-Side Configuration
Because the proxy is configured as non-transparent the client side should also be configured. This can be done by specifying by hand the location of the proxy in the setting of the browser, in order to access the Internet. In this article the proxy is set for a Firefox browser. Click the menu button and open Preferences. Go to Advanced > Network and click on Settings...
On the Connection Settings tab it appears, choose from the list Configure Proxies to Access the Internet the Manual proxy configuration. Add your HTTP Proxy IP address (in this case 192.168.0.15, which is the Endian IP address) and Port number (8080). Select the box Use this proxy server for all protocols and then click OK.
You can test your configuration now by browsing the Internet from the Green network and testing different user logins (admin and general user) to verify the appropriate content filtering profiles are being applied.
You should also be able to view all the web traffic in real-time by going to Logs and Reports > Live Log and select the "HTTP Proxy" log to view. You'll notice in both the live log viewer and regular proxy logs (pictured above) that you can identify the username for individual traffic which can help you in monitoring users web behavior.
Troubleshooting
- Make sure to use the proxy in non-transparent mode (which is a mandatorywhen using the web proxy with authentication the only supported mode is non-transparent).
- Verify if the server configuration data is correct (see Section Prerequisites above).
- Check if the clock is synchronized with the ad server. This is done by using the linux command wbinfo -u from the SSH command line. If the command returns an error it means that the Endian is not joined to the AD server.
- You receive the error message AD/LDAP server not found. To fix this problem, go to Proxy > DNS > DNS routing then click on Add new custom nameserver. Here insert the domain name and the IP address of the DNS server in your domain.
Connecting to AD using LDAP
This method can be used either with the HTTP Proxy or the various VPN services (OpenVPN, IPsec XAUTH, and IPsec L2TP). The graphic interface is identical for both the HTTP Proxy and the VPN services, but here we show the VPN, which requires an additional step to be performed.
Configuration of the external Authentication Server
To start the configuration, go to VPN > Authentication > Settings. If you have not yet configured any external authentication server, you will see the following screen:
Click on Add a new Authentication server to open the editor and start the configuration. This page is identical to the one shown when configuring LDAP authentication with the HTTP Proxy.

Here you can enter the following data to configure the server:
- A name to identify the server (in our example, companyldap).
- The type of the authentication (LDAP/Active Directory).
- The URI of the LDAP server, either as FQDN or IP address (10.8.1.21).
- The LDAP server type, in our case Active Directory. Alternative options are Generic and Novell eDirectory, which require options analgo to the next ones.
- The LDAP username, the username required to access the LDAP server and retrieve the groups and users. (administrator@services.example.com: note that it must be fully qualified!)
- The LDAP password correspondent to the user. You can tick the checkbox on the right-hand side to show the password's characters.
- The user base DN and group base DN, both with the same CN=Users,DC=services,DC=example,DC=com value.
Optionally, you can also tick the Limit to specific groups option. This allows anly the selected groups to be used for the authentication on the Endian device.
Click on Change to save the configuration, then on Apply in the green callout that will appear. If everything works, you will see the new server in the list.

At this point, you should map the authentication server to the necessary service. This can be done from VPN > Authentication > Settings in the Authentication server mappings table. Edit the service needed and add to it the authentication server configured.
Now, you can go in the users or groups tab and find there the users and groups retrieved from the LDAP server. If you have already defined any local users, they show up along with those from the LDAP server.

Troubleshooting the connection
You can connect to the VPN server using the credentials for one of the users retrieved from the LDAP server. To see the connection established you can go to Status>VPN connections where all the users connected to the VPN are shown.
You can also use the following command from the command line:
root@endian:~ # show openvpn
OpenVPN server connections of eos-devel.localdomain at 12:31 on 2017-04-27
Remote Address Virtual Address Connected Since Client Name
192.168.150.3 10.2.128.103 2017-04-27 12:20:13 alexmaria
Also, you could verify the connection from the computer you connect to the VPN by checking if the IP received is from the zone to which the VPN is linked to (in the screenshot below the IP retrieved is form the Green Zone of the device).
While setting up the authentication server you could encounter the following error messages, when trying to retrieve the users and groups from the server:
- Can't contact LDAP server! - This error usually is caused by a wrong URI. Verify that the URI is valid (either as FQDN or IP address).
- Invalid credentials! - This error might appear because the username given is not correct, or it is not fully qualified. Another problem of this could be that the password provided is wrong.
- No such object! or LDAP Operations Error - These two errors can be solved by introducing the correct LDAP user base DN and LDAP group base DN.
In my installation EFW 3.2.4 does not have the options "group" and "settings" in VPN > Authentication. Exist a way to active this screens?
I am using version 3.0.0. How often does the proxy synchronize group list with AD controllers?