Applies to platform: UTM 5.0, 4i Edge 5.0
Updated on: 1st March 2017
Applies to platform: UTM 6.0, 4i Edge 6.0
Updated on: 23 Jan 2023
This lesson guides you in the set up of two OpenVPN server instances on an Endian Appliance. The intended use case is a company that wants to keep separate VPN traffic for their administrative and development departments (We will make one routed and one bridged instance for the sake of completeness).
Preliminaries
To complete successfully this lesson you need:
- An Endian UTM Appliance or an Endian 4i Edge Appliance.
- Your system should have a multiple core CPU (we have three in our use case) if you plan to have multiple instances running concurrently. Indeed, having more instance running than cores available reduces the performances of the OpenVPN server and is in general not suggested.
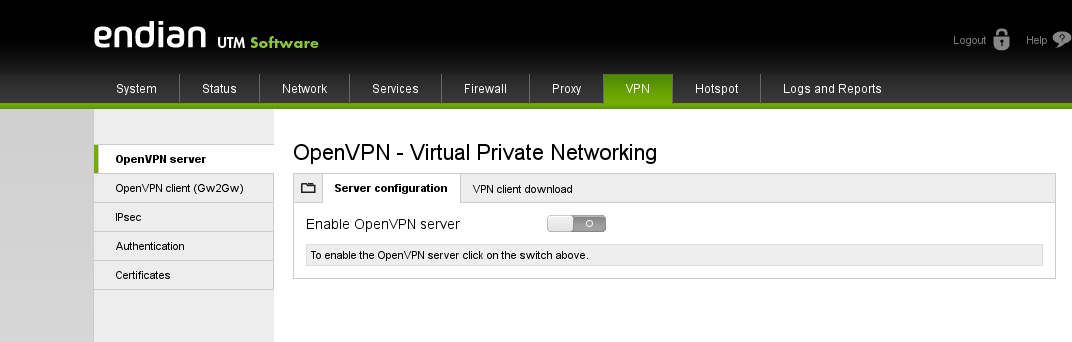
Start the OpenVPN Server
To start the OpenVPN server simply go to VPN > OpenVPN server, and click on the gray switch:
To start the OpenVPN server simply go to VPN > OpenVPN server > Server configuration, and click on the gray switch:
If you never used before the VPN module, you will have to wait a bit while your Endian Appliance generates the root and host certificates needed by the server.
Manage the Default Instance
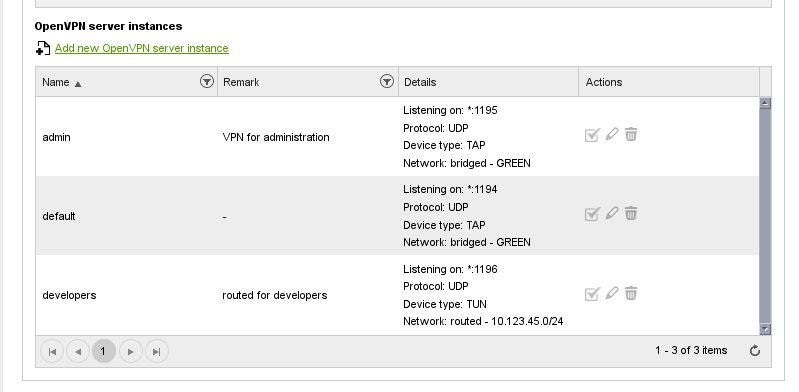
After this process has completed, you will see the page containing the global settings of the server and the default server instance, at the bottom, configured with the most used settings, i.e., listening on port 1194, using UDP protocol and TAP device. Moreover, the default instance has a bridge to the GREEN zone of the Endian Appliance.
After this process has completed, you can navigate to VPN > OpenVPN server > Server Instances where you will find the default server instance (created automatically) configured with the default settings, i.e., listening on port 1194, using UDP protocol and TAP device. Moreover, the default instance has a bridge to the GREEN zone of the Endian Appliance.
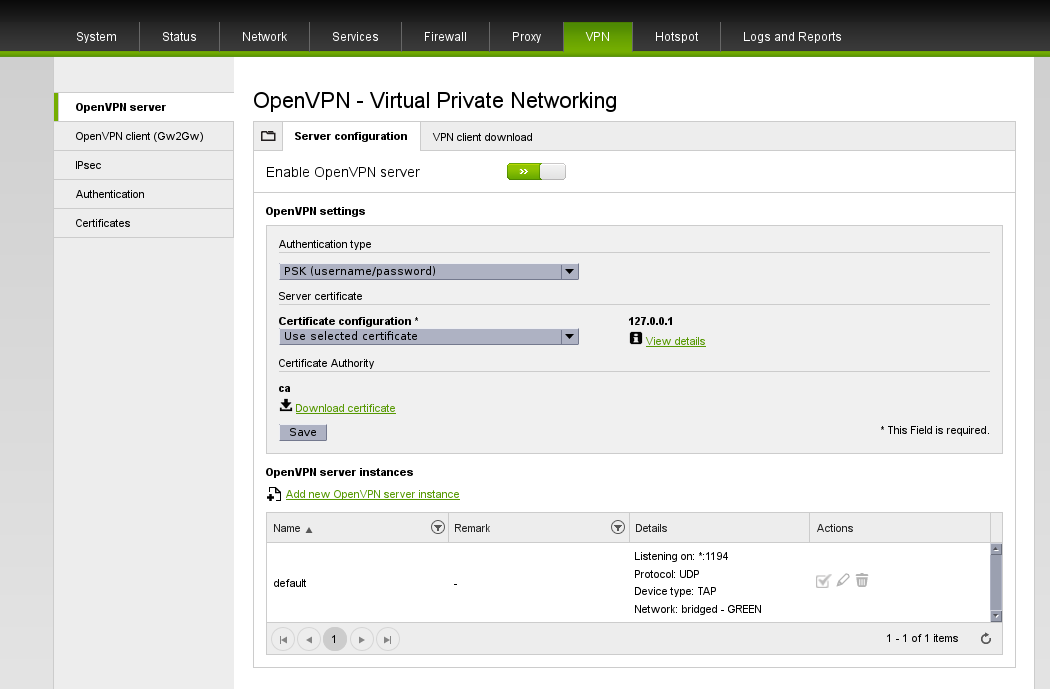
The available settings concern:
- the type of authentication, with choices between single-factor (PSK + username only or certificate only) or two-factors (PSK + username and certificate)
- The server certificate to use. If you prefer to use your own certificate, or create a new one, several options can be chosen:
- Generate a new certificate from scratch.
- Use selected certificate, shown on the right-hand side of the drop-down menu.
- Use an existing certificate.
- Upload a certificate.
- Upload a certificate signing request.
You can find more details about these options in the online reference manual. You can now create new server instances by clicking on the Add new OpenVPN server instance link above the table.
If you would like to define a bridged OpenVPN server instance, continue reading the next section, while for a routed one, skip it and go to the subsequent one.
Create a New Bridged Instance
Note
By default, the instance configuration consists of a TAP device, a bridge to the GREEN zone, and UDP protocol. If you prefer to set up a routed instance, skip to next section.
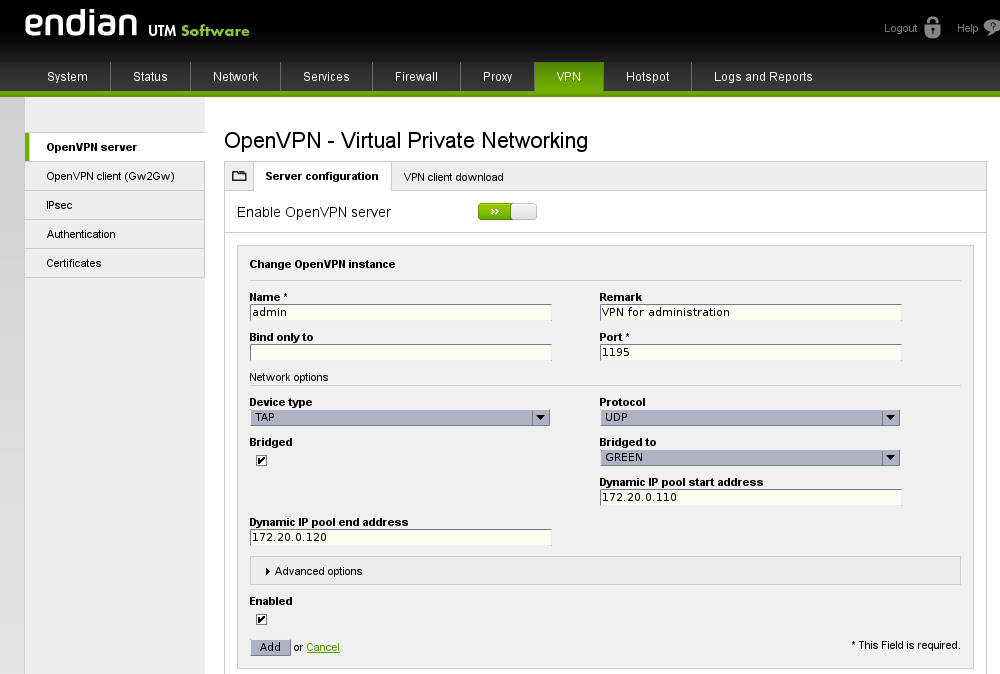
In this example, we configure only a few options:
- The connections' name (admin).
- A remark, recalling the connection's purpose (VPN for administration).
- The port this instance will listen to (1195), waiting for incoming connections.
- The IP pool dedicated to this connection, which ought to fall within the interval of the GREEN zone. Since in the example the GREEN zone has subnet 172.20.0.0/24, you can define the IP Pool starting at 172.20.0.110 and ending at 172.20.0.120.
Warning
The IP pool chosen for the Bridged VPN instance needs to be within the same zone range but needs to be outside the IP range of the DHCP server in the same zone too (if enabled). Therefore, you might need to shrink the DHCP server IP range of the same zone in order to avoid overlapping with the IP pool configured in this bridged VPN instance.
Optionally, you can select some advanced options, common to all clients that will connect using this VPN server. Click on Advanced options to reveal a panel showing a couple of options.

In our scenario, we add only two options:
- A private nameserver 172.20.0.200, used to resolve IP addresses within the internal network.
- A whole sub-network, 192.168.0.120/24, and a route to it (automatically added), reachable by clients.
Remember to tick the two checkboxes under the labels Push these nameservers and Push these networks to actually have the client receive the options.
Now, click on Add to complete the set up and store the new configuration, then click on Apply to restart the OpenVPN server and let the new instance immediately accept new connections.
To set up a new routed instance, proceed to the next section, otherwise skip to the last section below.
Create a new routed instance
After clicking on the Add new OpenVPN server instance link, we change some standard configuration options.
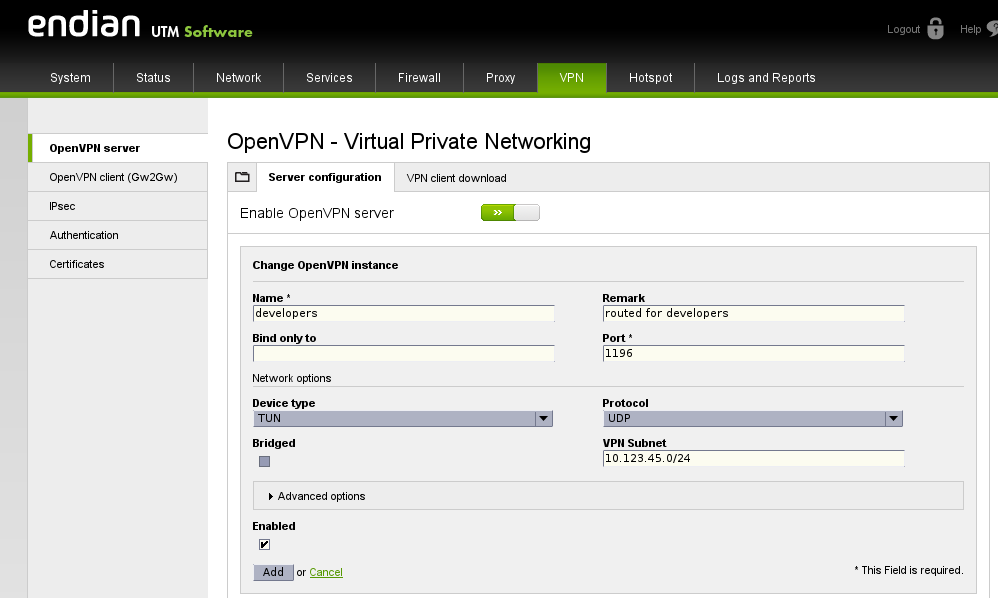
In particular, we enter these values:
- The connection's name (developers).
- A remark (routed for developers).
- The port this instance will listen to (1196), waiting for incoming connections.
- The device shall be changed to TUN: This changes also the option right below, replacing the two textboxes for the IP pool definition with one called VPN subnet.
- In the VPN Subnet textfield we enter a new, separated subnet (10.123.45.0/24) that will account for all IP assigned to clients.
To configure advanced options for the clients, click on Advanced options and refer to the previous section for directions.
Now, click on Add to complete the set up and store the new configuration, then click on Apply to restart the OpenVPN server and let the new instance immediately accept new connections.
Verify That All Instances Run
After you have created a new instance, you will be brought back to the initial Server configuration page: At the bottom you see the list of the server you defined.
Connecting clients to the OpenVPN server
After the successful installation of the OpenVPN server, it is possible to configure clients to connect to the server. The available possibilities are:
- A single user that needs to connect from a remote site (the so-called Roadwarrior connection). This set up is described in this howto.
- If you use Linux, you can setup a Roadwarrior connection by using the Network Manager, like explained in this howto.
- A remote network behind a gateway should be connected and accessible from the network behind the server (the Net2Net or Gw2Gw connection).This set up is described in this howto.
I could also add, for the last step, to verify from command line:
root@endian:~ # ps www -u openvpn
PID TTY STAT TIME COMMAND
4467 ? Ss 0:00 /usr/sbin/openvpn --config /etc/openvpn/openvpn.1.conf
4560 ? Ss 0:00 /usr/sbin/openvpn --config /etc/openvpn/openvpn.2.conf
4717 ? Ss 0:00 /usr/sbin/openvpn --config /etc/openvpn/openvpn.3.conf
and (to verify which server has which config file)
root@endian:~ # head -1 /etc/openvpn/openvpn.1.conf
; daemon configuration for server default (1_0) server #1
root@endian:~ # head -1 /etc/openvpn/openvpn.2.conf
; daemon configuration for server admin (2_0) server #2
root@endian:~ # head -1 /etc/openvpn/openvpn.3.conf
; daemon configuration for server developers (3_0) server #3