Applies to Platform: UTM 5.0 and 6.0
This lesson will illustrate the necessary steps to configure a very simple Net-to-Net IPSec VPN tunnel between two Endian appliances.
Configuration Example
The diagram above is a simple illustration of the configuration example covered in this guide. We'll be creating a Net-to-Net connection to allow communication between the two internal Green (LAN) networks of each Endian device.
Enable the VPN Server (Site A)
From the main menu, select VPN > IPSec and then check the box to enable IPsec.
Add a VPN Connection (Site A)
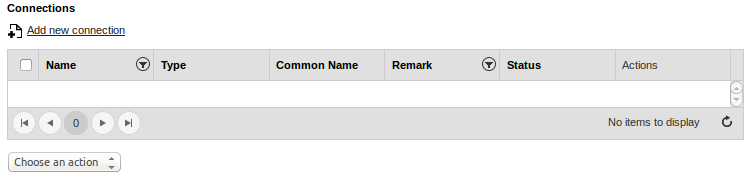
Under VPN > IPSec > Connections menu, click the Add new connection button to create a new connection.
Configure VPN Settings (Site A)
In the next screen, which it will be as the following:
we can configure the main settings for this VPN connection:
- Select a name for your VPN connection.
- Select Net-to-Net as the Connection type.
- Provide an authentication method. In this case we're using pre-shared key as this is the simplest and most common method.
- Select which Internet interface you want to use for this specific connection. In our case, it will be the uplink interface.
- Provide the remote VPN subnets belonging to site B and which you want to connect to (192.168.20.0/24).
- Provide the public IP or hostname of the remote Endian UTM device of site B (10.2.128.156).
warning
After such steps, proceed to modify some advanced settings by clicking on Advanced. The following screen will be shown:
Note
Set the parameters for both phases, exactly as shown on the picture above, by modifying the followings:
- IKEv2 has to be selected for IKE version.
- Only AES (256 bit) has to be selected for both IKE and ESP encryption.
- Only SHA2 256 has to be selected for both IKE and ESP integrity.
- Only DH group 14 (2048 bit) has to be selected for both IKE and ESP group type.
In addition to these, set also Starts the connection if traffic is detected as Connection startup.
Click Save to finish.
Enable the VPN Server (Site B)
From the main menu, select VPN > IPSec and then check the box to enable IPsec.
Click Save to continue.
Add a VPN Connection (Site B)
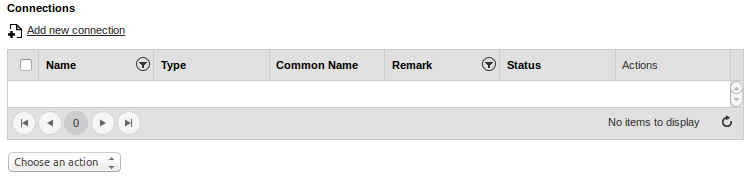
On the Endian (Site B) device, under VPN > IPSec > Connections menu, click the Add new connection button to create a new connection.
Configure VPN Settings (Site B)
In the next screen, which it will be as the following:
we can configure the main settings for this VPN connection:
- Select a name for your VPN connection.
- Select Net-to-Net as the Connection type.
- Provide an authentication method. In this case we're using pre-shared key as this is the simplest and most common method.
- Select which Internet interface you want to use for this specific connection. In our case, it will be the uplink interface.
- Provide the remote VPN subnets belonging to site A and which you want to connect to (192.168.5.0/24).
- Provide the public IP or hostname of the remote Endian UTM device of site A (10.2.128.193).
After such steps, proceed to modify some advanced settings by clicking on Advanced. The following screen will be shown:
Set the parameters exactly as shown on the picture above, by modifying the followings:
- IKEv2 has to be selected for IKE version.
- Only AES (256 bit) has to be selected for both IKE and ESP encryption.
- Only SHA2 256 has to be selected for both IKE and ESP integrity.
- Only DH group 14 (2048 bit) has to be selected for both IKE and ESP group type.
In addition to these, set also Starts the connection if traffic is detected as Connection startup.
Click Save to finish.
Verify Connection (Site A & B)
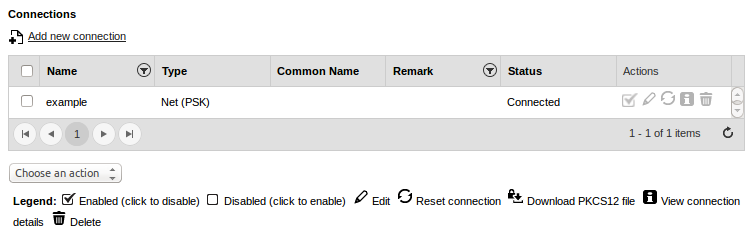
On the Site A VPN device, you should the "Status" go from CLOSED to CONNECTED, which indicates a successful connection.
Test VPN Connectivity (Site A & B)
Now you should be able to successfully test all internal access to remote devices (resources) from both sides of the VPN tunnel. Anything from a simple ICMP ping to an RDP session or remote web server should be accessible across the tunnel.
Comments