Applies to Platform: UTM 2.4, UTM 2.5
Last Update: 04 June 2014
Note
This lesson explains how to block, with the Endian UTM Appliance, facebook, twitter, and other sites that use SSL. Two different approaches will be shown in this lesson: Using an Access Policy rule in the HTTP Proxy, and using the DNS proxy
The first apporach should be used when the HTTP proxy is set to Non-Transparent, while the second approach is suitable for cases where the HTTP proxy is not enabled, or is enabled in Transparent mode.
1. Create an Access Policy to Block HTTP/HTTPS Sites.
This method is useful only when the HTTP Proxy is enabled in Non-Transparent mode. From the web GUI select from Menubar > Proxy > HTTP > Access Policy > Add Access Policy.

In the Access Policy Editor, configure as follows the various options:
- Source: The places where the clients will be subjected to the rule, which can be ANY, Zone, Network/IP, or MAC Address.
- Destination: The places that you want to block. In this case, the domains facebook.com and twitter.com. Write one domain per line, remember the starting dot if you want to : .facebook.com and .twitter.com.
- Access Policy: Deny access, for the rule to block traffic to the domains.
- Position: First, to make sure that this rule take precedence over other rule, which possibly allow access.
- Policy status: Click on the checkbox Enable policy rule to activate the rule.
- The remaining options may keep their default values.
Note
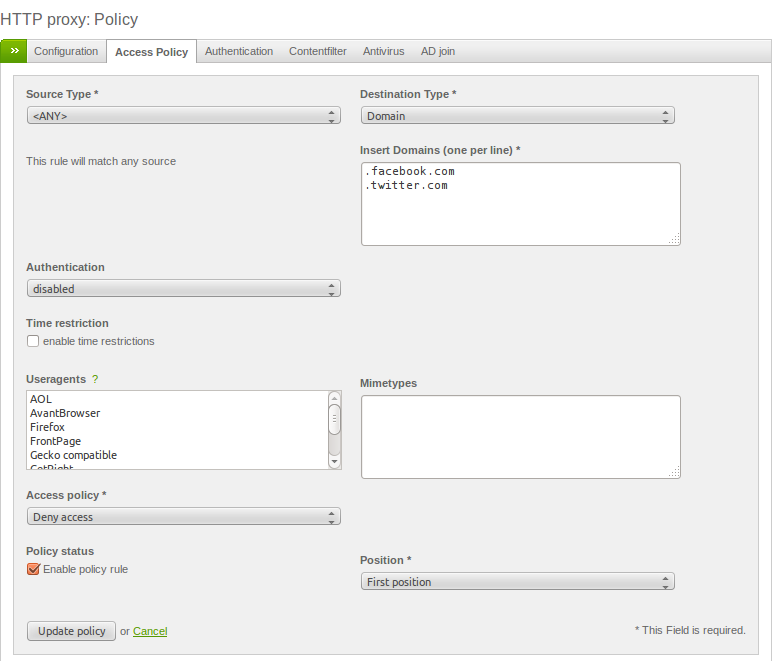
Finally, click on Update policy to save the new rule. After a few seconds, all services are reloaded and the new rule begins working.
2. Create a Rule in DNS Proxy
This method is useful ONLY in two situation:
- you have the HTTP Proxy set in transparent mode (This method can intercept only HTTP traffic)
- you don't have HTTP proxy enabled.
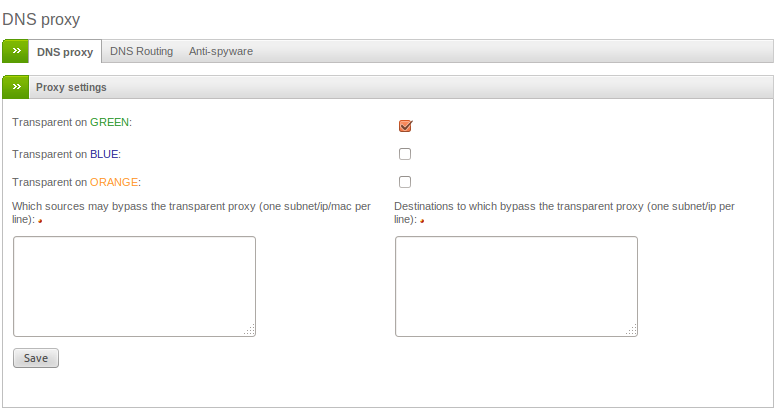
From the web GUI go to Menubar > Proxy > DNS. Click on the checkboxes next to the Transparent on GREEN, BLUE, ORANGE, depending on which zones you want to create the rule into, then clik on Save.
Now, go to the Anti-spyware tab and insert in the textbos under the Blacklist domains label all the domains that you want to be blocked (ex. facebook.com) and click on Save.

Note
i have UTM on a virtual Lab as virtual Machine,
can i i apply this settings to my ISP Wifi setting throught my VM UTM ?
Hi, I found very useful explanation to block some domains that have access both http and https.
To block access https (eg Facebook) have used the technique number 2, that "Create a Rule in DNS Proxy" and it works perfectly! But it is possible to exclude a computer / IP address from this block?
With the technique "Create a Rule in DNS Proxy" locks all clients on the network and I can not exclude anyone ... Is there a way to make it accessible https site (eg Facebook) only to a certain ip or my computer?
Thanks for your attention.
A DNS proxy rule is valid for all workstations behind it, so no exclusion is possible.
Escribe texto o la dirección de un sitio web, o bien, traduce un documento.
Cancelar
Hi
Ultrasurf passes this security and to navigate in Facebook, such as blocking the brute force attack on the endian.
First approache works for IE, but not for Chrome. Any suggestions?
Hello,
I have used endian 2.4.1 for many years with https url blocking with success.
Now I'm doing a new 3.0.5 firewall for replacing the old, but HTTPS url blocking doesn't work, it's block http url but NOT https. I have checked and the browser used for testing use proxy for both http and https. It's this normal? It's changed the logic of url blocking? I'm forced to use the new https proxy (with all related problems with certs) ?
Thank you for your good products!
Daniele.
Any one who can help me I need to block all the websites and slow only certain websites
Any easy way to do it and I tried to do it by adding access policy but suddenly the clients can access internet