Functionality Description
With two-factor authentication, Endian VPN security is dramatically increased. Instead of just requiring a username and password, an additional piece of information is required that is generated by a token. In this case the authentication procedure is a combination of something you know (username and password) and something you have (time-based token). This prevents unauthorized VPN access even in the event your username and password are stolen or compromised since the attacker must also have the token information to successfully authenticate.
General Description
There are a variety of tokens and token manufacturers in the field. Each of them implements their own algorithm and they all require you to implement their technology on the server-side. Most of these providers already now offer hardware solutions (i.e. physical tokens that display a code) and software solutions (e.g. smartphone applications).
Fortunately enough there is an open standard that has been defined and that can be used without having to rely on third party software licenses or hardware tokens. It is called the Time-based One-Time Password (TOTP) and has been released as RFC 6238.
User Setup
On the user side a smartphone application or any other device that is compatible to TOTP can be used. A number of compatible smartphone applications is already available. They are all available for free (other applications exist as well, this is only a short list):
|
Platform |
Apps |
|
Android |
|
|
iOS |
|
|
Windows Mobile |
In order to generate the one-time passwords, each user has to setup an account in the application. There are two ways for setting up the accounts:
-
create the account manually by copying the provided shared secret
-
taking a picture of the QR Code containing the account information from inside the application
This secret key will be used for all future logins. The application generates a new one-time password every 30 seconds – and since the algorithm is time-based this does not even require an Internet connection. In Figure 1 the interfaces of the above listed mobile applications can be seen.
Switchboard Setup
On the Switchboard side the defined algorithm will be implemented and integrated into the authentication module. To be able to achieve this the implementation must be done for two different subsystems of the Switchboard:
-
OpenVPN
-
Web Interface
Technical Implementation
OpenVPN One-Time Password Configuration
In order to use the two factor authentication, a one-time password authentication provider must be added and the provider scope must be configured to use this new provider.
In Figure 2 One-time password authentication server configuration the provider configuration for OpenVPN is shown (the configuration for IPsec L2TP and XAuth is identical). From the VPN > Authentication page a new authentication server has to be added and configured as following:
|
Configuration option |
Value |
|
Type |
One-Time Password |
|
User information provider |
Local |
|
Password provider |
Local or any remote password provider |
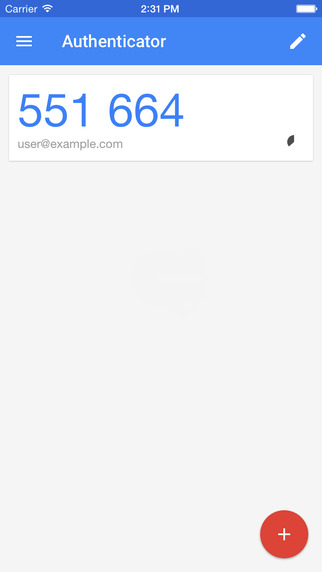


Figure 1 Google Authenticator, FreeOTP and Microsoft Authenticator interfaces showing generated tokens
In this example a local password provider has been used to verify user names and passwords. However, the two-factor authentication implementation is also compatible with other password providers, e.g. RADIUS or LDAP. When used in combination with the Switchboard the user information provider field should be set to “switchboard”.

Figure 2 One-time password authentication server configuration
After the creation of the authentication server, the OpenVPN authentication server mapping must be configured as shown in Figure 3. In this case the configured otp authentication server must be selected as backend instead of “local”.
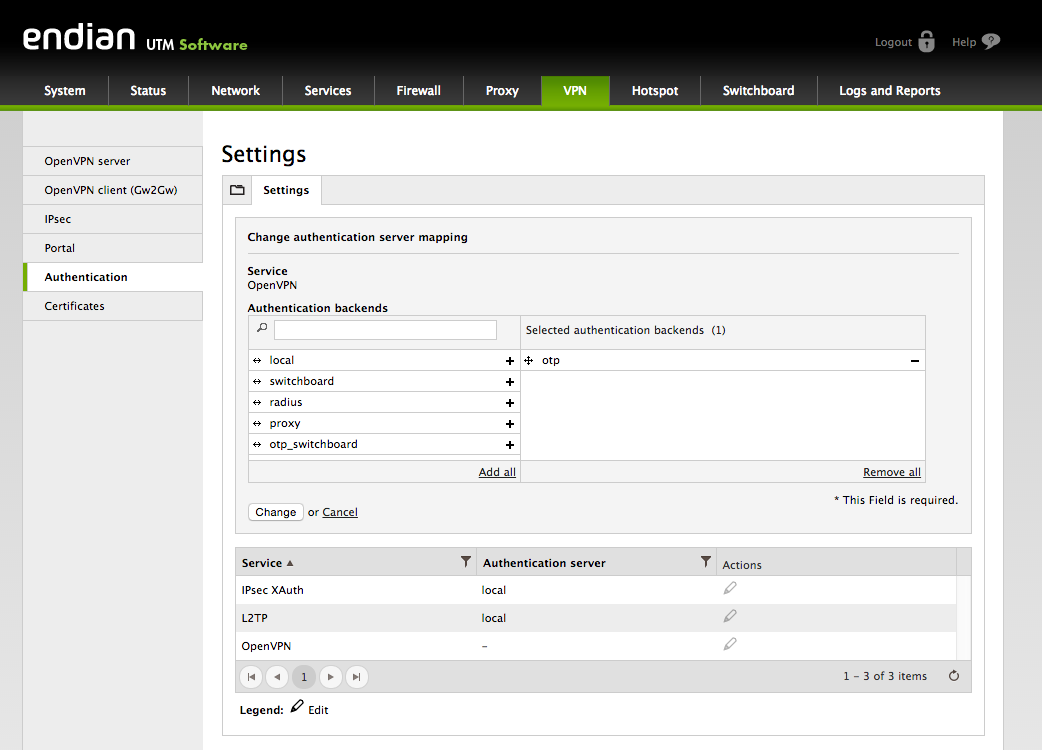
Figure 3 OpenVPN authentication server mapping configuration
Switchboard One-time Password Configuration
The Switchboard configuration (Figure 4) is similar to the one for OpenVPN. Again it is possible to select “switchboard” or any external provider in the password provider field.
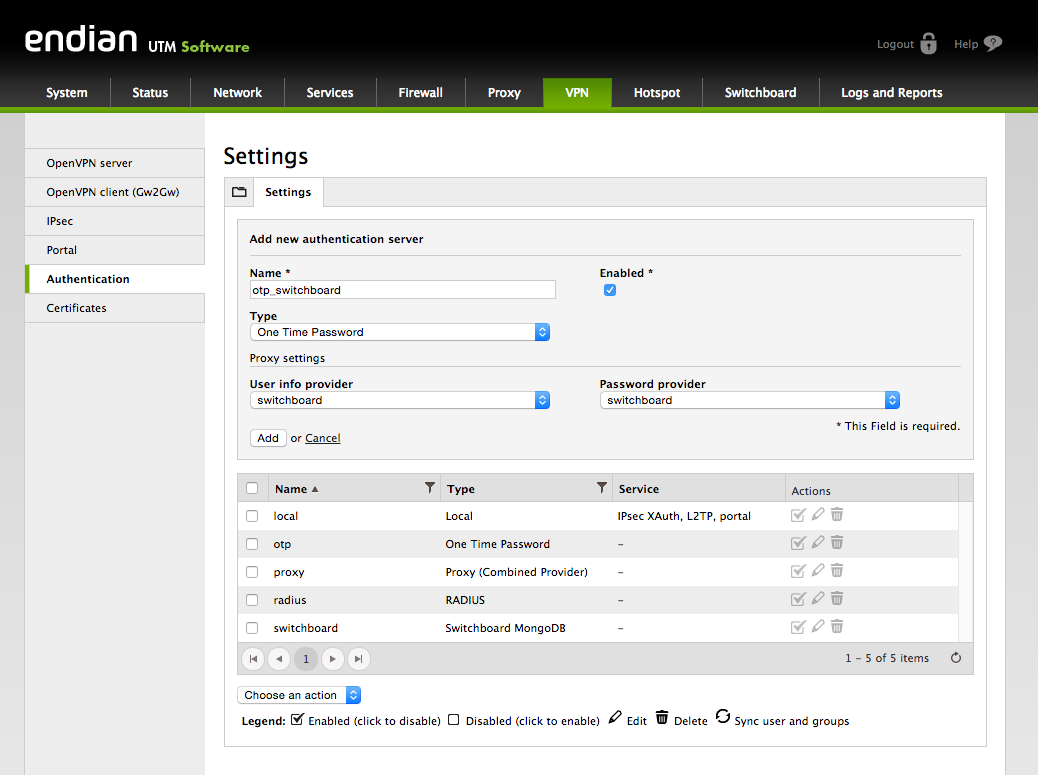
Figure 4 OTP authentication server configuration for the Switchboard
When configuring the Switchboard’s authentication server mapping it is necessary to select both “apache” and the one-time password authentication provider to make sure the system administrator can access the Switchboard’s pages just like any other Switchboard user.
User Configuration
The user configuration workflow is shown below in Figure 5.
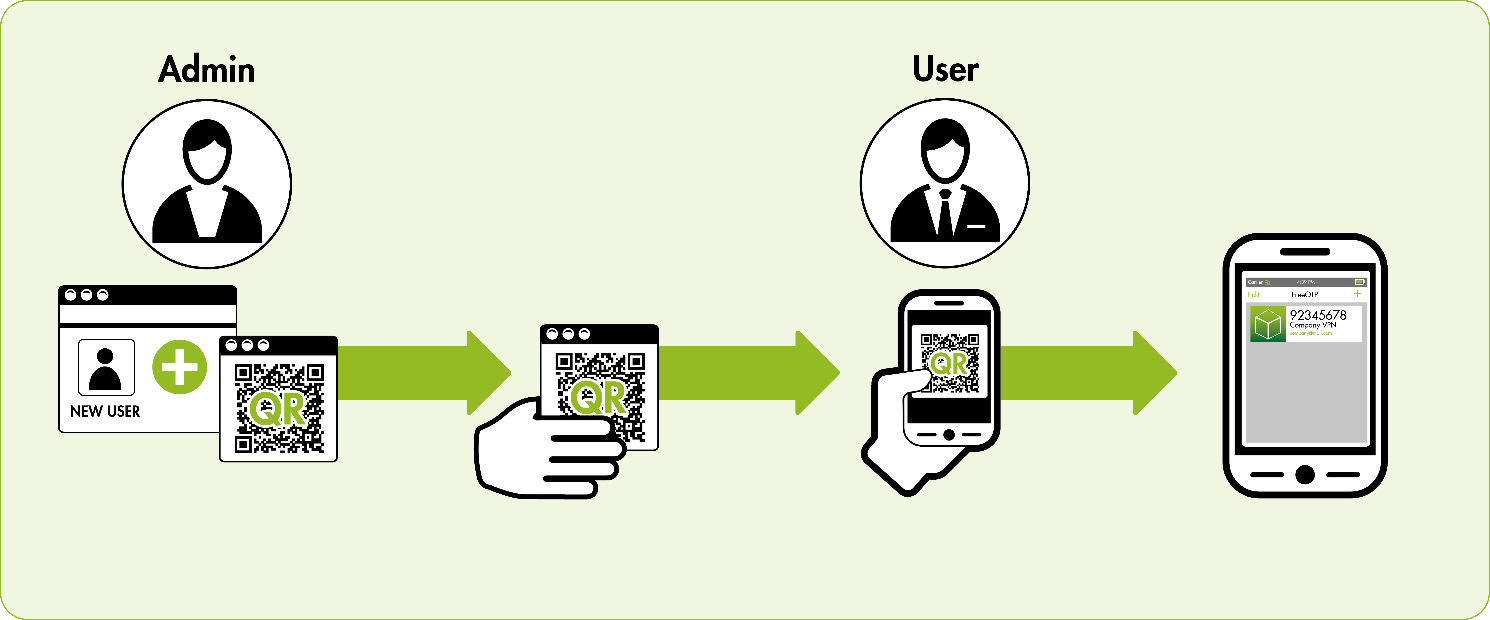
Figure 5 User configuration workflow
Once both OpenVPN and the Switchboard have been configured to support the two-factor authentication a new field will appear in the user editor. Figure 6 shows the “One-Time Password secret” that is automatically generated. If you do not see a secret listed in the field, you can create one by clicking "Generate new secret". This read only field contains the 80-bit shared secret for the given user that is required to synchronize the smartphone with the Switchboard.
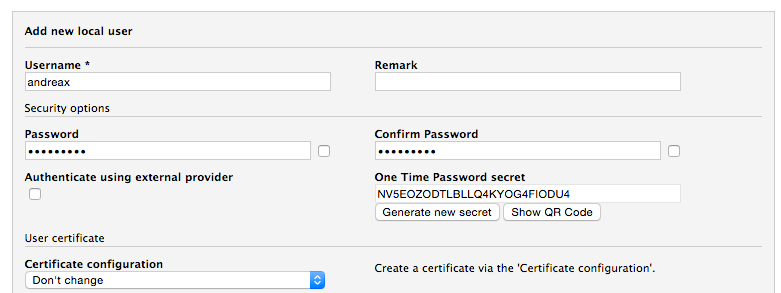
Figure 6 VPN User editing form
It is possible to generate a new secret (invalidating a previously configured App account) and displaying the QR code to auto-configure the smartphone application (shown in Figure 7). The QR code can also be downloaded through the context-menu when clicking with the right mouse button on the image.
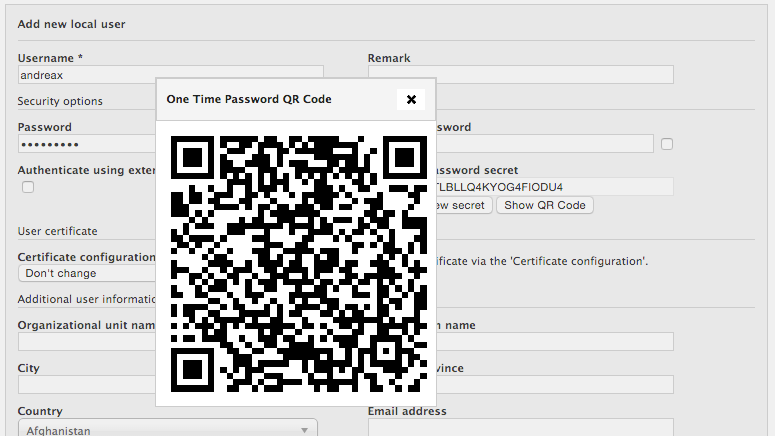
Figure 7 QR code to be used for app configuration
User Login
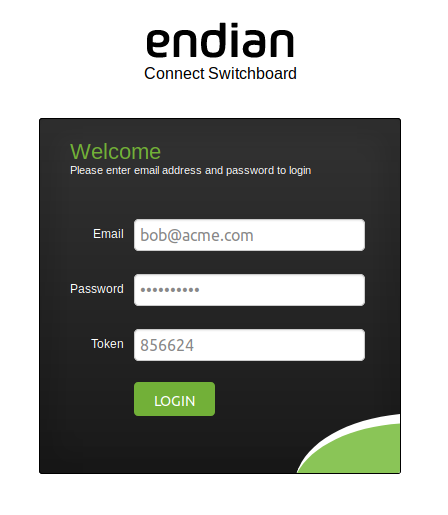
After having added a One-Time Password secret to the user the login procedure will slightly change. The user must now also provide a valid token provided by the mobile application when logging into the Switchboard.
Depending on the access medium the step to connect are:
From Switchboard Web portal:
- Enter the OTP token in the dedicated field and press LOGIN
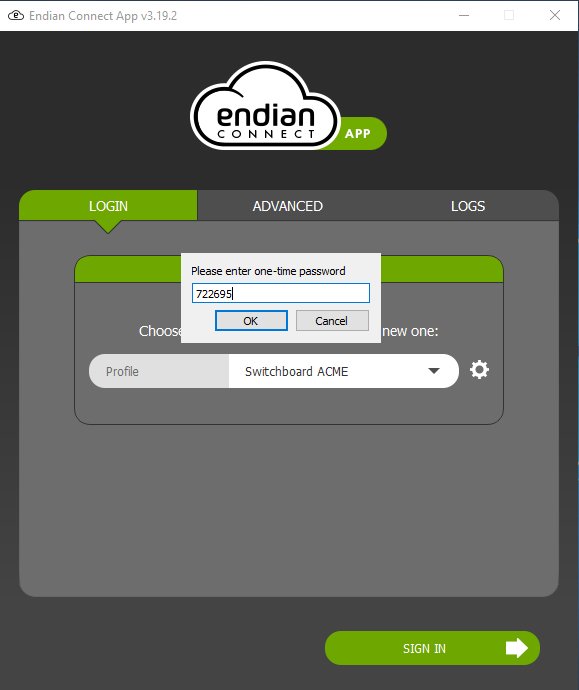
From the Endian Connect App:
- In the connection profile when you configure the details for the connection to the Switchboard, turn on the field "One-time password enabled" at the bottom of the form.
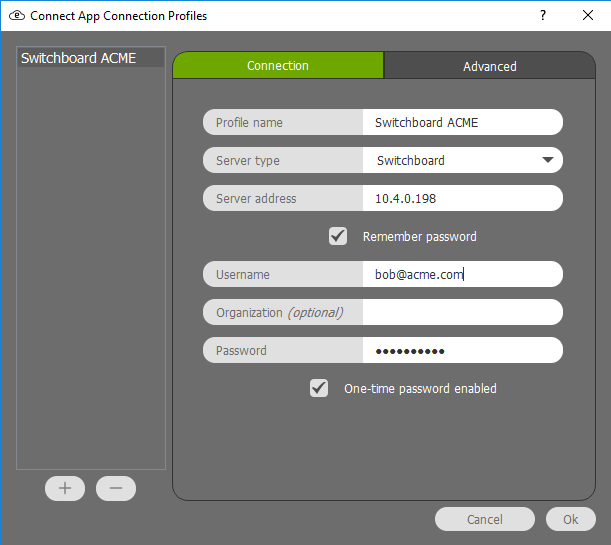
- In the main screen select the profile and press "SING IN".
- A pop up will be display asking for the OTP token from the application. Enter the token and press "OK"
From third-party clients:
- User opens the VPN client application and prepares to login.
- Prior to typing the user password, the user opens the OTP application on their mobile device (links provided under "User Setup")
- To login, the user types their normal password with a space followed by the OTP token (password<space>OTP token) displayed on their mobile device all in the password field of the VPN client software
Comments